
Solutions
Device Fingerprinting
Advanced device fingerprinting technology to identify and track devices across sessions and detect suspicious behavior patterns.
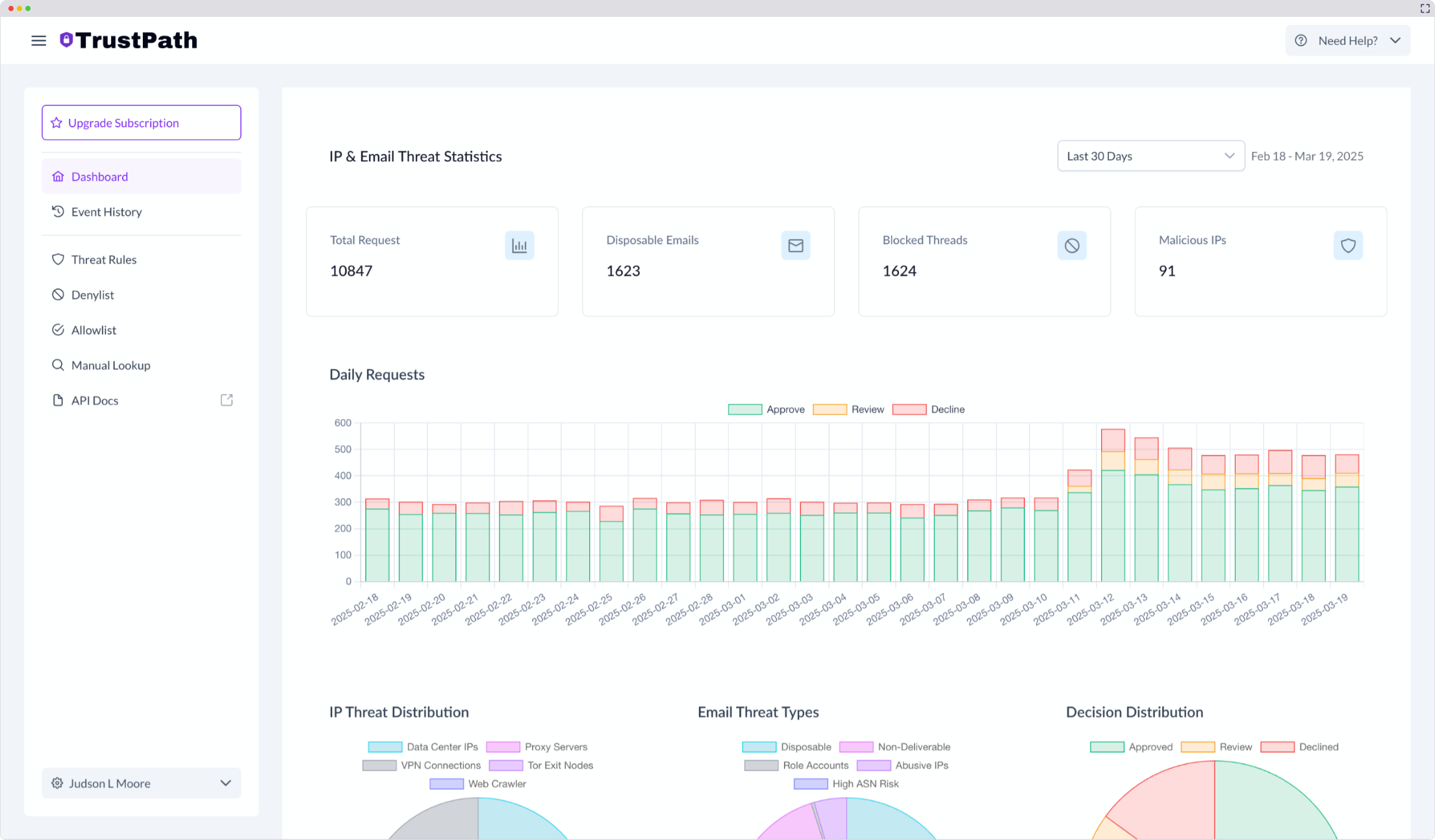
OUR TECHNOLOGY
How TrustPath protects your transactions
Analyze
Real-time transaction monitoring and risk assessment.
Detect
Fraud pattern recognition and behavioral analysis.
Prevent
Automated blocking of suspicious transactions while allowing legitimate ones.
Device Fingerprinting
Behavior Recognition
Create unique digital identifiers for devices and browsers to enhance security and prevent fraud without compromising user experience.
- Generate unique device hashes based on hardware
- Create browser fingerprints that persist across sessions
- Provide cross-browser compatibility for consistancy

Benefits
Key Benefits of Fingerprinting
Our fingerprinting technology provides powerful fraud prevention capabilities while maintaining a seamless user experience.
Enhanced Fraud Detection
Identify suspicious activities by tracking device and browser characteristics across multiple sessions and accounts.
Account Takeover Prevention
Detect unusual login attempts from unfamiliar devices or browsers, even when credentials are valid.
Multi-Account Abuse Prevention
Identify users creating multiple accounts to abuse freemium services or promotional offers.
Seamless Integration
Easy implementation through our JavaScript SDK with both npm package and CDN options.
Privacy-Friendly Approach
Collect only necessary device information without compromising user privacy or requiring personal data.
Trust
Security & Compliance
We maintain high security standards and aim to comply with major industry regulations and frameworks.


Protect Your Business
Schedule a demo with our fraud prevention experts to see how TrustPath can secure your transactions. Get personalized insights into your specific fraud risks.
- • Need help assessing your fraud exposure?
- • Want to understand our detection capabilities?
- • Looking for custom fraud prevention strategies?
Engin Yöyen
Co-Founder